2 Risk Management
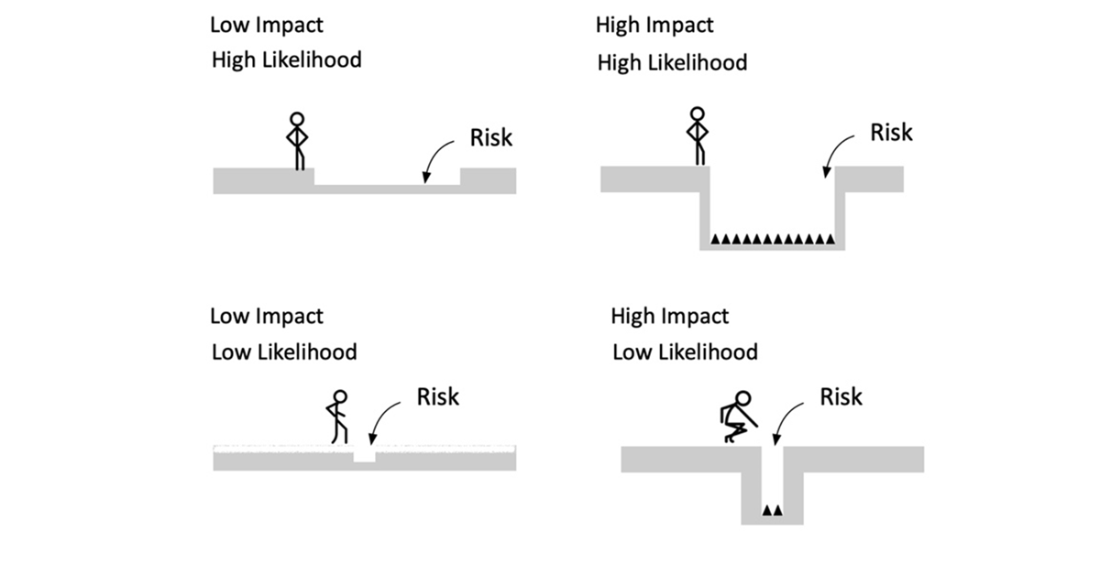
Organizations cannot protect every asset against every threat with unlimited resources, so this chapter frames cybersecurity as a risk-based discipline. It defines risk as the combination of how much harm an event could cause (impact) and how likely it is to occur (likelihood). Impact spans more than monetary loss, covering operational disruption, regulatory penalties, reputational damage, and effects on third parties; likelihood is often estimated using practical ranges rather than precise probabilities. By combining these dimensions—often visualized in a risk matrix or expressed mathematically—teams can compare vulnerabilities and focus first on those that present the greatest overall risk.
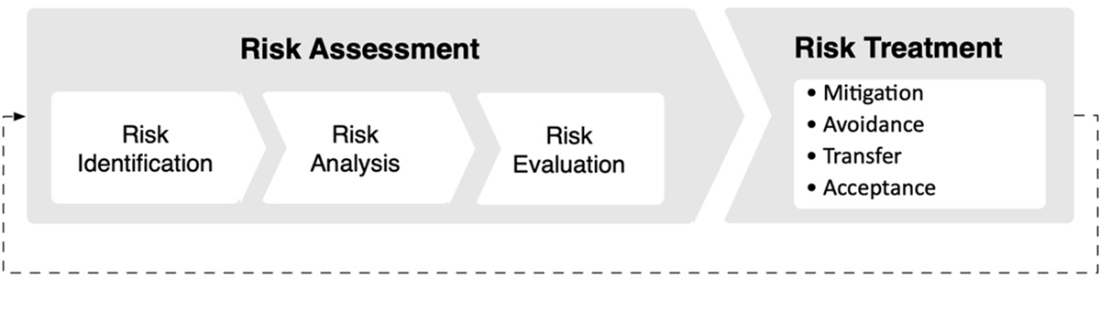
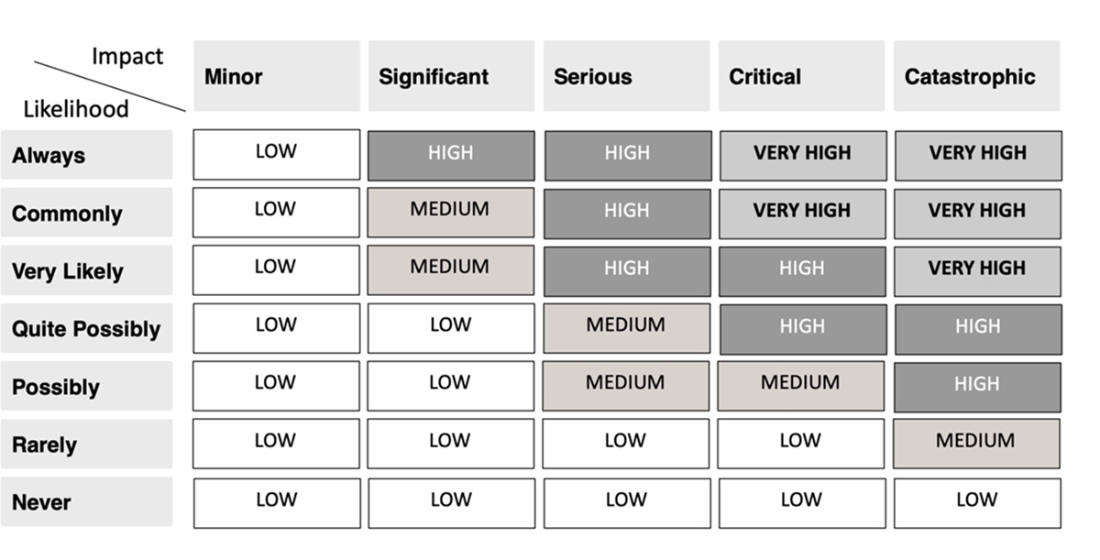
Risk management is presented as an ongoing process with two stages: assessment and treatment. Assessment begins with risk identification, which relies on accurate and regularly updated asset inventories and clear assignment of asset and risk owners. Risk analysis then estimates impact and likelihood using quantitative methods (for example, asset value, exposure factor, single loss expectancy, annualized rate of occurrence, and annualized loss expectancy) or qualitative methods (descriptive scales and a risk matrix), or both. Risk evaluation prioritizes the results, generally breaking ties in favor of higher-impact scenarios and elevating any threat to human safety, so that limited resources address the most consequential risks first.
Risk treatment selects proportionate strategies—mitigate, avoid, transfer, or accept—guided by cost/benefit considerations, organizational risk appetite, and specific risk tolerances for business functions. Because no control set eliminates all exposure, residual risk must be acknowledged and either accepted or further reduced, and teams should recognize that new controls can introduce new risks. Effective practice requires documented treatment plans, clear communication with risk owners, integration with daily operations, and continual reassessment as assets, threats, and business priorities evolve, ensuring security investments deliver the greatest reduction in risk aligned to organizational goals.
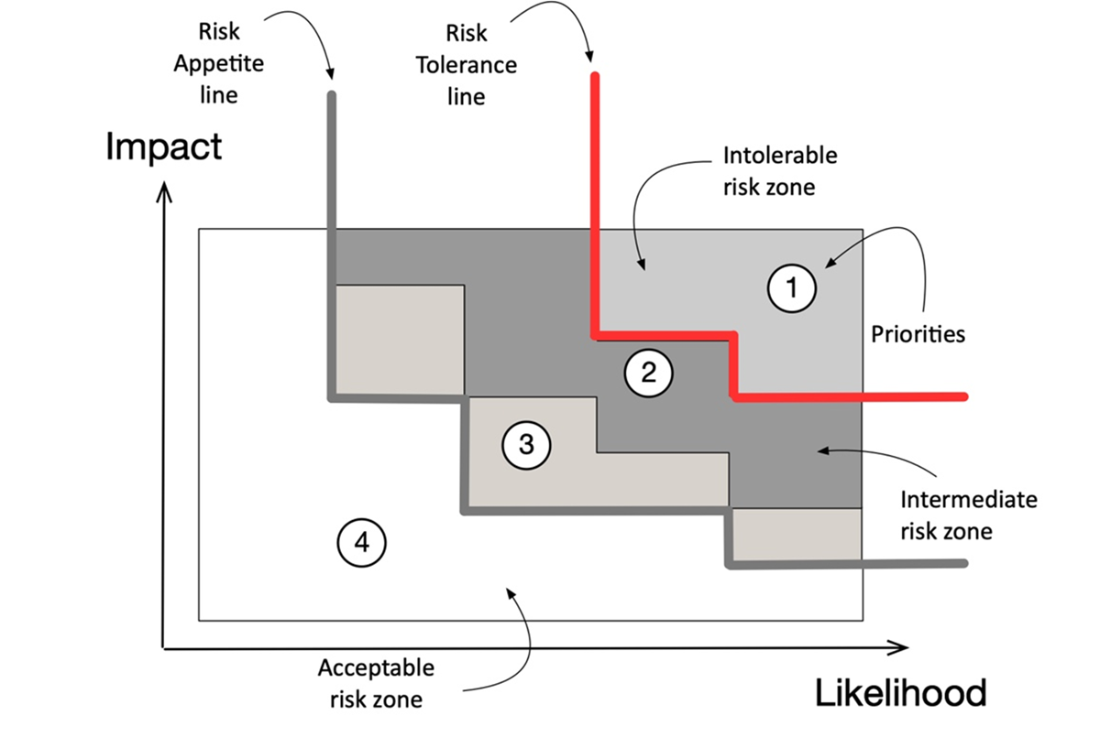
Illustration of the risk in terms of likelihood and impact
Risk as function of likelihood and impact
Illustration of the risk management process
A risk matrix displaying the level of risk as a function of the values of likelihood and impact
Risk prioritization quadrants according to likelihood and impact
Answers to Review Questions
- The correct answer is B. The purpose of any insurance is to transfer risk from one party to another and this process is called risk transference. The insurer is obligated to compensate the insured for a loss caused by an unexpected event over a specified and mutually agreed upon period of time.
- The correct answer is A. Risk management is a proactive process of identifying, assessing and prioritizing risks. Appropriate controls are then selected and implemented to reduce or mitigate the potential impact of identified risks. On the other hand, eliminating all risks is impractical, minimizing implementation costs can expose an organization to unnecessary risk, and focusing solely on reactive countermeasures runs counter to the principles of comprehensive risk management.
- The correct answer is D. Risk acceptance is a risk management strategy in which an organization chooses not to implement controls to address a risk, but instead accepts the risk and its potential consequences. This doesn't mean that the company ignores the risk; rather, it has made a conscious decision to accept it after considering the costs and benefits.
- The correct answer is A. Residual risk helps organizations understand the remaining level of risk they face after implementing their chosen controls and countermeasures, enabling them to make informed decisions about whether additional action is needed or whether the remaining risk is acceptable. None of the other options accurately describe the concept of residual risk.
- The correct answer is A. Risk mitigation involves implementing strategies to limit the impact or likelihood of threats occurring. Risk acceptance, on the other hand, is a conscious decision to acknowledge a risk but not take immediate action.
 Become ISC2 Certified in Cybersecurity ebook for free
Become ISC2 Certified in Cybersecurity ebook for free